Advances in the performance and adoption of solar photovoltaics
Author: admin
-

Advances in the performance and adoption of solar photovoltaics
-
Prolonged social media use is not fundamentally problematic in a Hungarian representative study
Whiting, A. & Williams, D. Why people use social media: a uses and gratifications approach. Qual. Mark. Res. Int. J. 16, 362–369 (2013).
Kozan, H., Baloğlu, M., Kesici, Ş. & Arpacı, İ….
Continue Reading
-

How your brain chemistry rewards hard work
How your brain chemistry rewards hard work
Continue Reading
-
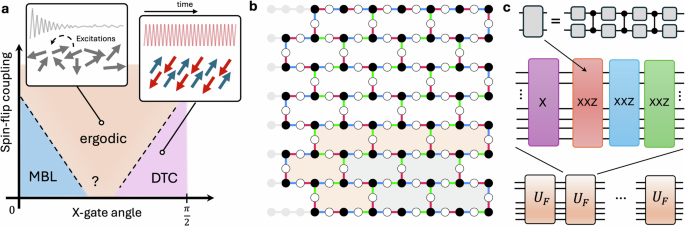
Realization of two-dimensional discrete time crystals with anisotropic Heisenberg coupling
Srednicki, M. Chaos and quantum thermalization. Phys. Rev. E 50, 888 (1994).
Google Scholar
Rigol, M., Dunjko, V. & Olshanii, M. Thermalization and its mechanism for generic…
Continue Reading
-

Pesticide cocktails negatively affect soil biodiversity
Pesticide cocktails negatively affect soil biodiversity
Continue Reading
-
Machine learning approach for wheat variety identification using single-seed imaging
Pourreza, A., Pourreza, H., Abbaspour-Fard, M.-H. & Sadrnia, H. Identification of nine Iranian wheat seed varieties by textural analysis with image processing. Comput. Electron. Agric. 83, 102–108 (2012).
Continue Reading
-

Justice as a measure of energy transition success
Justice as a measure of energy transition success
Continue Reading
-
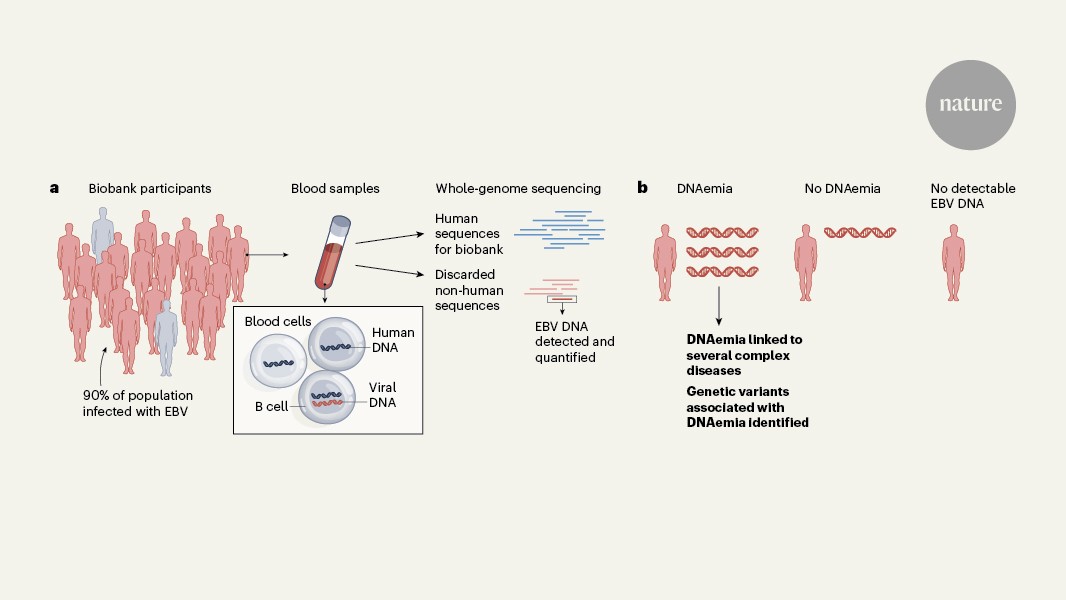
Scraps of viral DNA in biobank samples reveal secrets of Epstein–Barr virus
Nyeo, S. S. et al. Nature https://doi.org/10.1038/s41586-025-10020-2 (2026).
Google Scholar
Meirhaeghe, M. R. & Balfour, H. H. Jr. J. Clin. Virol. 180, 105854 (2025).
…
Continue Reading
-
Deep learning based individual identification and population estimation of the yellow spotted mountain newt (Neurergus derjugini)
Karczmarski, L., Chan, S. C. Y., Chui, S. Y. S. & Cameron, E. Z. Individual identification and photographic techniques in mammalian ecological and behavioural research—Part 2: field studies and applications. Mamm. Biol. 102, 1047–1054 (2022).
Continue Reading
-
A self-evolution cyber attack scheme generation system for cybersecurity evaluation
Konsta, A.-M., Lafuente, A. L., Spiga, B. & Dragoni, N. Survey: Automatic generation of attack trees and attack graphs. Comput. Security 137, 103602 (2024).
Zhong, M., Lin, M., Zhang, C. & Xu,…
Continue Reading
